Ransomware Landscape in Q1 2026: Consolidation and Key Players
Overview of Q1 2026 Ransomware Activity
The first quarter of 2026 revealed a ransomware ecosystem undergoing significant structural changes. While attack volumes remained historically high, a clear trend toward consolidation among dominant groups emerged. This article examines the key findings, including the stabilisation of victim numbers, the rise of new players, and the shifting balance of power among ransomware operators.

Key Findings at a Glance
- Consolidation after peak fragmentation: The top 10 ransomware groups accounted for 71% of all Q1 2026 victims, a sharp reversal from the fragmentation seen in Q3 2025. The ecosystem is now converging around fewer, more dominant operators.
- Volume stabilisation at high levels: Data leak sites (DLS) recorded 2,122 victims, the second-highest Q1 on record. This indicates a plateau after years of growth.
- Qilin’s continued dominance: Qilin remained the most active ransomware operation for the third consecutive quarter, posting 338 victims.
- The Gentlemen’s rapid ascent: This group jumped to third place, increasing victim counts from 40 in Q4 2025 to 166 in Q1 2026.
- LockBit 5.0 returns: LockBit posted 163 victims, securing fourth place and confirming its comeback.
Volume Trends: A New Normal
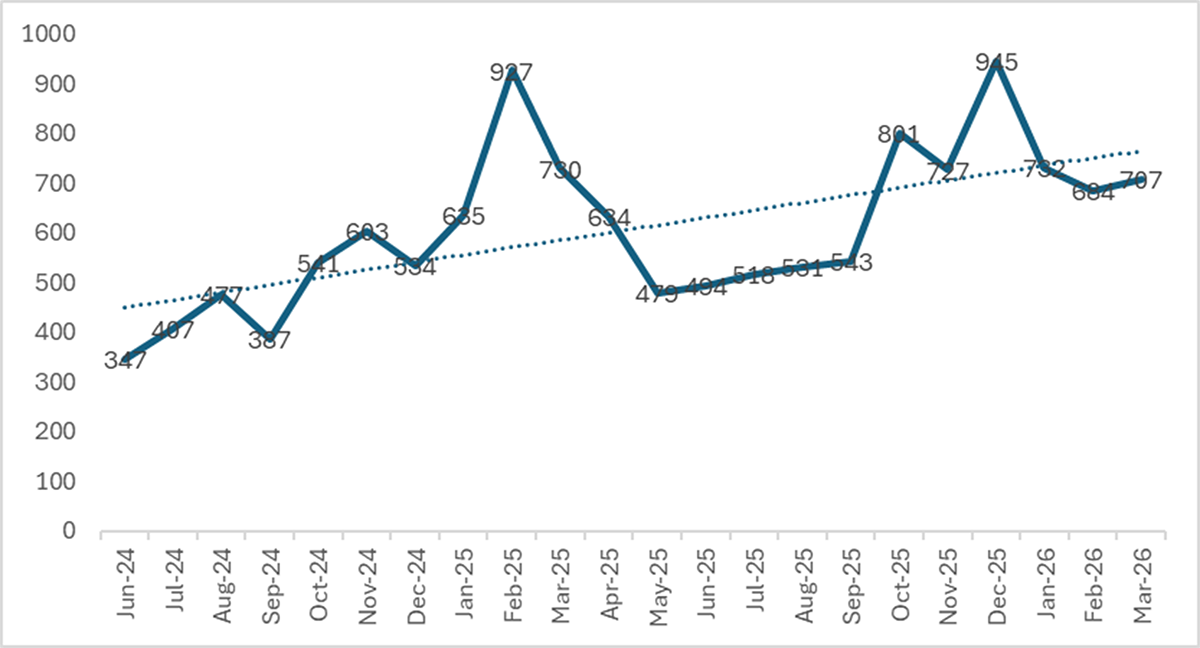
During Q1 2026, we monitored over 70 active data leak sites that collectively listed 2,122 new victims. This represents a 12.2% decline from the record 2,416 victims in Q4 2025, yet it remains the second-highest Q1 ever—117% above Q1 2024’s 977 victims. Monthly figures were notably consistent: January saw 732 victims, February 684, and March 706, averaging 707 per month. This stability suggests that ransomware operations have reached a sustained high plateau.
Year-over-year comparison shows a 7.1% drop from Q1 2025’s 2,285 victims. However, this is misleading because Q1 2025 was inflated by Cl0p's massive Cleo exploitation campaign, which contributed roughly 390 victims in a single burst. Excluding Cl0p from both periods reveals a 5.3% increase: 1,894 victims in Q1 2025 versus 1,995 in Q1 2026. The underlying growth trend persists, even as dramatic spikes subside.
From Fragmentation to Consolidation
The most notable structural shift in Q1 2026 is not attack volume but the concentration of operators. After two years of steady fragmentation—active groups growing from 51 in Q1 2024 to a peak of 85 in Q3 2025, and the top 10 share falling from 68% to 57%—the ecosystem has reversed course decisively.
Top 10 Groups Now Control 71% of Victims
In Q1 2026, the top 10 groups accounted for 71.1% of all DLS-posted victims, the highest concentration since Q1 2024. The number of active groups shrank from 85 to 71. Fourteen groups that were active in Q4 2025 disappeared entirely, while 21 new names appeared. This churn indicates a Darwinian environment where only the most capable operations survive.
Key Players in Q1 2026
Qilin: Steady Dominance
Qilin retained its position as the most prominent ransomware operation for the third quarter running, posting 338 victims. Its consistent performance underlines its operational maturity and broad targeting strategy.
The Gentlemen: The Breakout Story
The Gentlemen emerged as the breakout story of Q1 2026. Their victim count soared from 40 in Q4 2025 to 166, propelling them to third place globally. This rapid growth signals an aggressive expansion and effective attack methodology.
LockBit 5.0: A Confirmed Comeback
LockBit posted 163 victims in Q1 2026, climbing to fourth place. After a period of decline, the release of LockBit 5.0 has reinvigorated the group, demonstrating the resilience of established ransomware brands.
Implications for Organisations
The consolidation around fewer, more capable groups means that defence strategies must focus on the most prevalent threats. With volumes stabilising at historical highs, organisations should expect a persistent, high-pressure environment. The disappearance of small groups and emergence of new ones also highlights the need for continuous monitoring and adaptive security measures.
Conclusion
Q1 2026 marks a turning point in the ransomware landscape. Volumes have stabilised, but the ecosystem is restructuring around a small number of dominant groups. Qilin leads, while The Gentlemen and LockBit 5.0 illustrate the dynamic nature of this threat. Understanding these shifts is crucial for developing effective defences in the coming months.