Building an AI-Native Cyber Defense: A Step-by-Step Guide to Leveraging Frontier AI
Introduction
In the rapidly evolving landscape of cybersecurity, the latest advances from frontier AI labs like OpenAI, Anthropic, and Google DeepMind are not just technological milestones—they are catalysts for a fundamental shift. At SentinelOne, we have long believed that the future of defense lies in AI-native systems: platforms built from the ground up to operate at machine speed, autonomously detecting and responding to threats. This guide distills our decade of experience into actionable steps for organizations seeking to build or enhance their own AI-powered cyber defense. Whether you are a security architect, CISO, or DevOps leader, these steps will help you move from reactive to proactive security, leveraging frontier AI to outpace adversaries.
What You Need
- Established partnerships or access to frontier AI labs (e.g., OpenAI, Anthropic, Google DeepMind) for model insights and early capabilities.
- A behavioral AI platform capable of real-time analysis across endpoints, cloud, identity, data, network, and AI attack surfaces.
- Autonomous response automation that can execute actions at machine speed without human intervention.
- Continuous threat intelligence supply chain monitoring, and vulnerability prioritization capabilities.
- Cross-functional team with expertise in AI/ML, cybersecurity operations, and incident response.
Step-by-Step Guide
Step 1: Partner with Frontier AI Labs for Deep Insights
The first step is to forge strategic relationships with leading AI research organizations. SentinelOne has collaborated closely with OpenAI, Anthropic, and Google DeepMind for years, gaining meaningful insight into how advanced models evolve. These partnerships are not just about early access; they provide critical understanding of where models can create real impact in security. For example, frontier AI improves how defenders identify weaknesses, analyze complex systems, and reason about attack paths at scale. To replicate this, begin by engaging with AI labs through research collaborations, joint pilots, or membership in their security-focused programs. Regularly review model releases and incorporate learnings into your security stack. Learn how to integrate these insights in Step 2.
Step 2: Integrate Behavioral AI for Machine-Speed Detection
Frontier AI models are powerful, but they must be embedded into a behavioral AI framework that operates at machine speed. SentinelOne was built from day one to use behavioral AI for detection across all attack surfaces—endpoint, cloud, identity, data, network, and AI. This means analyzing patterns of behavior rather than static signatures, allowing the system to detect novel threats and zero-day exploits that traditional tools miss. To implement this step, deploy an AI-native platform that ingests telemetry from every layer of your environment. Train the AI on normal baselines and continuously update models with frontier AI advances. The goal is to identify anomalous behavior in milliseconds, not minutes.
Step 3: Implement Autonomous Response at Machine Speed
Detection alone is insufficient; you must also respond autonomously. In recent supply chain attacks like LiteLLM, Axios, and CPU-Z, the only effective countermeasure was autonomous response at machine speed. These attacks leveraged zero-day vulnerabilities in trusted agents and workflows, so manual intervention would have been too slow. Configure your platform to automatically contain threats—such as isolating endpoints, blocking processes, or revoking compromised credentials—based on AI-driven risk scores. Ensure your response actions are reversible and logged for post-incident analysis. Test autonomous playbooks regularly against simulated attacks. Next, learn how to bridge the gap between theoretical and operational risk.
Step 4: Bridge the Gap Between Vulnerability Disclosures and Real-World Risk
Frontier AI can uncover exponentially more bugs in software, but raw vulnerability counts rarely map to real-world risk. Many vulnerabilities are not meaningfully exploitable in live environments because of architectural layers, controls, mitigations, and runtime protections. The key is to prioritize what matters: understand actual conditions in your environment. Use AI to correlate vulnerability data with your specific configurations, asset criticality, and threat intelligence. Prioritize patches and mitigations based on exploitability in your context, not CVSS scores alone. This step ensures you stop real attacks, even when facing novel threats and zero days, rather than chasing every theoretical exposure.
Step 5: Continually Adapt to New Threats with Frontier AI Updates
The cyber threat landscape evolves daily, and so must your AI defenses. Frontier AI labs constantly release new models and capabilities—like improved reasoning or multistep attack path analysis. Establish a process to ingest these updates into your platform: retrain detection models, expand response playbooks, and adjust risk prioritization. For example, SentinelOne demonstrably expands its own ongoing efforts by incorporating learnings from each new frontier model release. Schedule quarterly reviews of new AI capabilities and run red-team exercises to validate their effectiveness against emerging attack techniques like supply chain compromises or AI-driven phishing. Finally, review our expert tips for long-term success.
Tips for Success
- Start small, then scale: Deploy AI-native defense in a contained environment first—such as your endpoint fleet—before expanding to cloud workloads and identity systems. Measure reduction in mean time to detect (MTTD) and mean time to respond (MTTR) as key success metrics.
- Maintain human oversight: While autonomy is critical, ensure security analysts have the ability to review and override automated actions when necessary. Use AI to augment human decision-making, not replace it entirely.
- Invest in supply chain visibility: As seen in the LiteLLM and Axios attacks, trusted suppliers can become vectors for zero-day exploits. Use AI to monitor third-party code, dependencies, and update channels for anomalous behavior.
- Share intelligence with peers: Collaborate with industry groups and AI labs to share anonymized threat data. Collective learning accelerates your defense as frontier AI evolves.
- Regularly test your autonomous response: Simulate zero-day scenarios (e.g., using red teams or bypass techniques) to ensure your platform can block novel threats without relying on signatures.
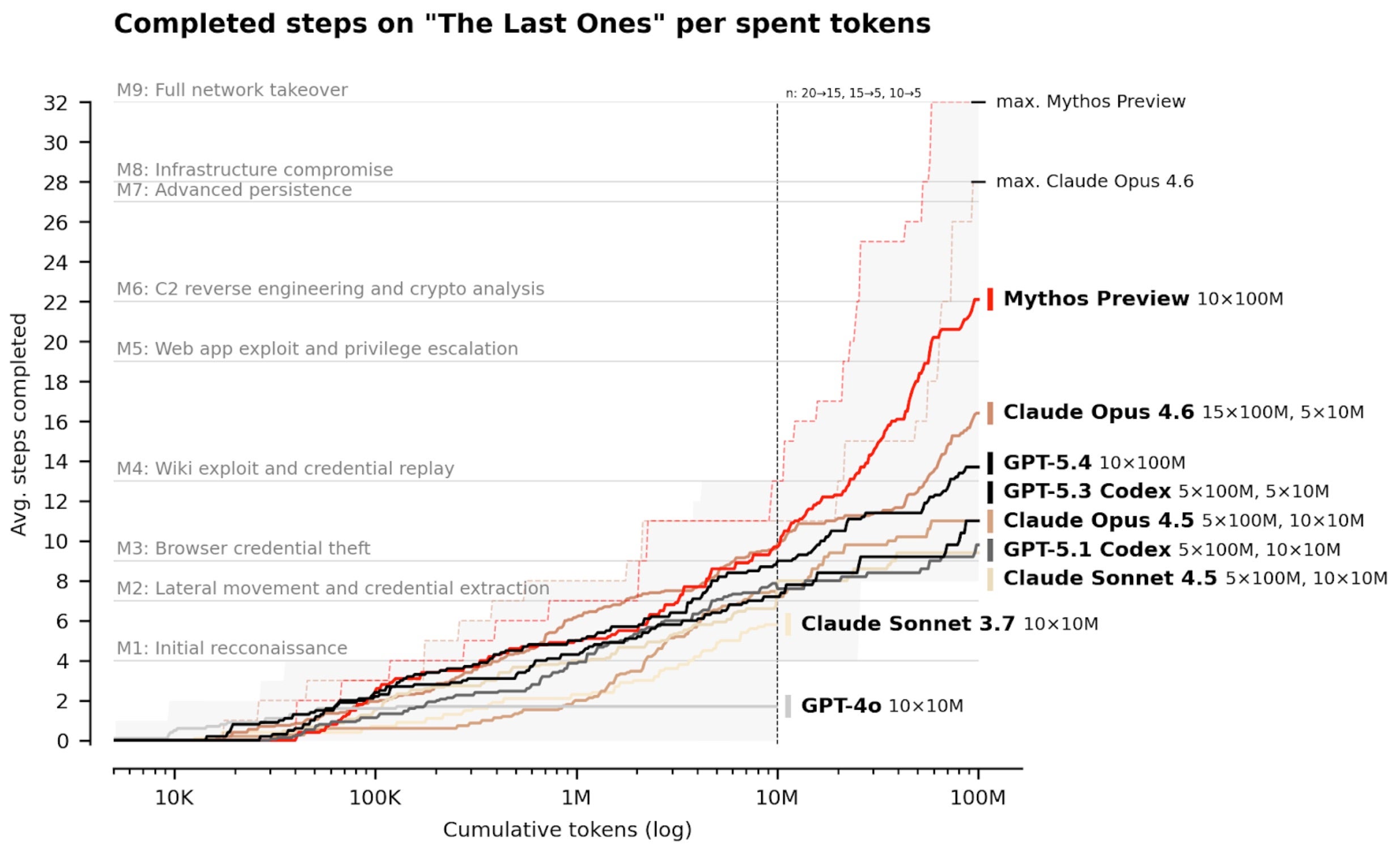
- Plan for adversarial AI: Attackers will also leverage frontier AI to find vulnerabilities faster. Your defense must outpace them by integrating the latest models before they are weaponized against you.
By following these steps, you can build a cyber defense that is not only reactive but anticipatory—operating at the speed of machines to stop the most advanced attacks. The future of cybersecurity is AI-native, and with the right approach, you can stay ahead of the curve.